In today's digital age, personal access tokens (PATs) have become a crucial component in managing secure access to platforms like Softr. Whether you're building custom applications, integrating third-party tools, or managing data, understanding the role of personal access tokens is essential. This article will provide a comprehensive guide to help you determine if you need personal access tokens for Softr and how they can enhance your workflow.
Personal access tokens act as secure keys that grant specific permissions to users, ensuring data integrity and protecting sensitive information. As more businesses and developers rely on platforms like Softr for no-code application development, understanding PATs becomes even more important. Let's dive deeper into why these tokens matter and how they fit into the broader context of app development.
By the end of this article, you'll have a clear understanding of whether personal access tokens are necessary for your Softr projects, how to implement them effectively, and how they contribute to better security practices. Let's get started!
Read also:Ignacia Michelson Desnudos A Comprehensive Exploration
Table of Contents
- What Are Personal Access Tokens?
- Softr Overview: A No-Code App Development Platform
- The Importance of Personal Access Tokens in Softr
- How Do Personal Access Tokens Work?
- When Should You Use Personal Access Tokens for Softr?
- Security Benefits of Personal Access Tokens
- Step-by-Step Guide to Setting Up Personal Access Tokens in Softr
- Alternatives to Personal Access Tokens
- Common Issues and Troubleshooting
- Best Practices for Managing Personal Access Tokens
What Are Personal Access Tokens?
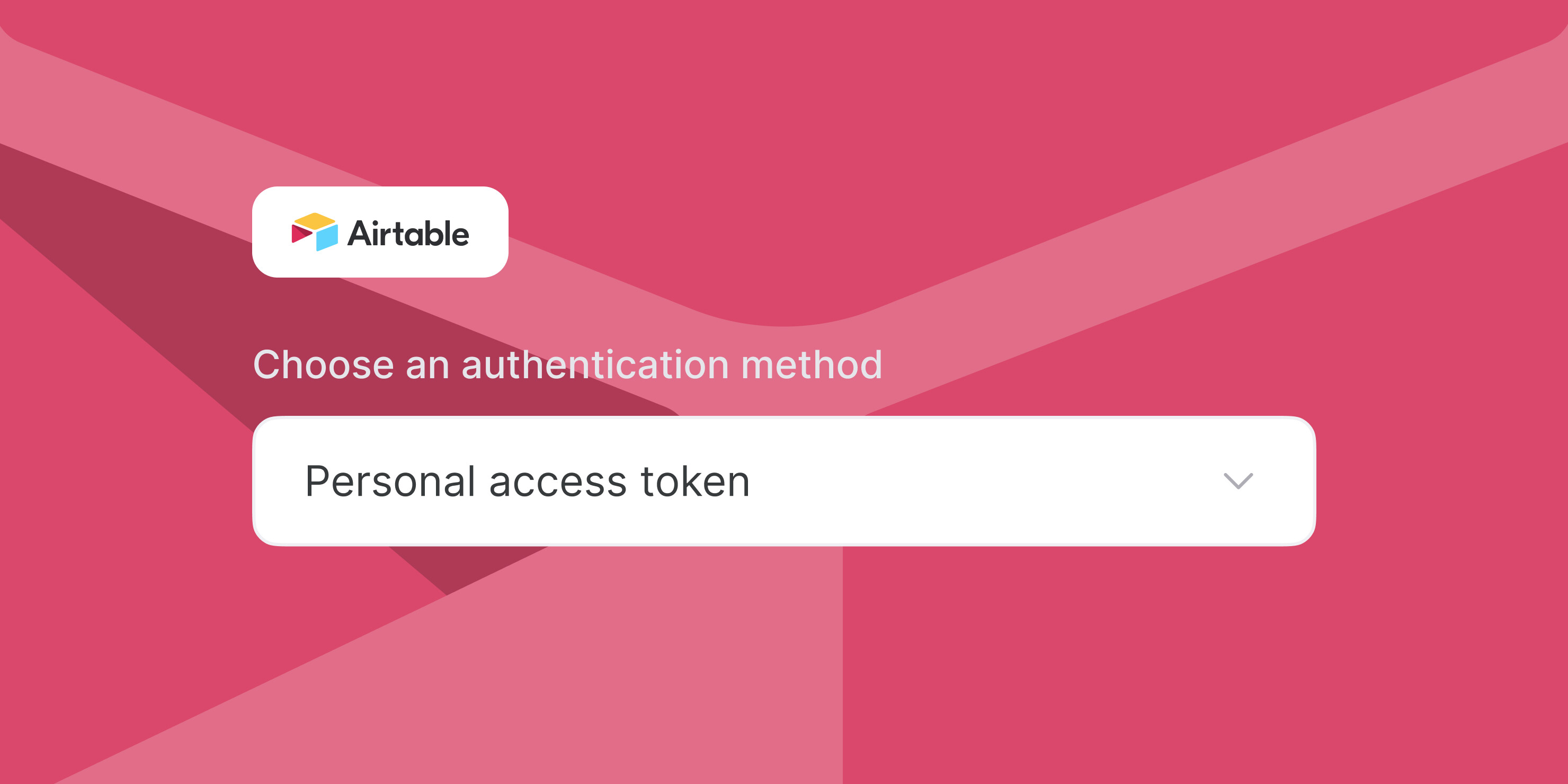
Personal access tokens (PATs) are unique strings of characters that serve as authentication credentials, granting specific permissions to access resources on a platform. Unlike traditional username and password combinations, PATs are designed for secure and automated access, making them ideal for API integrations, automated scripts, and third-party tools.
These tokens are typically generated within the platform's settings and can be assigned specific scopes or permissions. For example, in platforms like Softr, PATs can be used to manage user roles, control access to data, and integrate with external services securely.
Key Features of Personal Access Tokens
- Scoped Permissions: PATs can be configured to grant limited access to specific resources or actions.
- Revocable: Tokens can be easily revoked if they are compromised or no longer needed.
- Time-Limited: Many platforms allow you to set expiration dates for tokens, enhancing security.
Softr Overview: A No-Code App Development Platform
Softr is a powerful no-code platform that allows users to build custom applications without requiring extensive programming knowledge. It integrates seamlessly with platforms like Airtable, enabling businesses to create robust solutions for managing data, automating workflows, and improving productivity.
With Softr, users can create mobile and web applications, design custom dashboards, and integrate third-party tools to enhance functionality. However, as more integrations and automations are added, the need for secure access management becomes critical. This is where personal access tokens come into play.
Why Choose Softr?
- User-Friendly Interface: Softr's intuitive design makes it accessible for users of all skill levels.
- Scalability: The platform supports growing businesses with its flexible and scalable solutions.
- Integration Capabilities: Softr integrates with a wide range of tools and services, enhancing its functionality.
The Importance of Personal Access Tokens in Softr
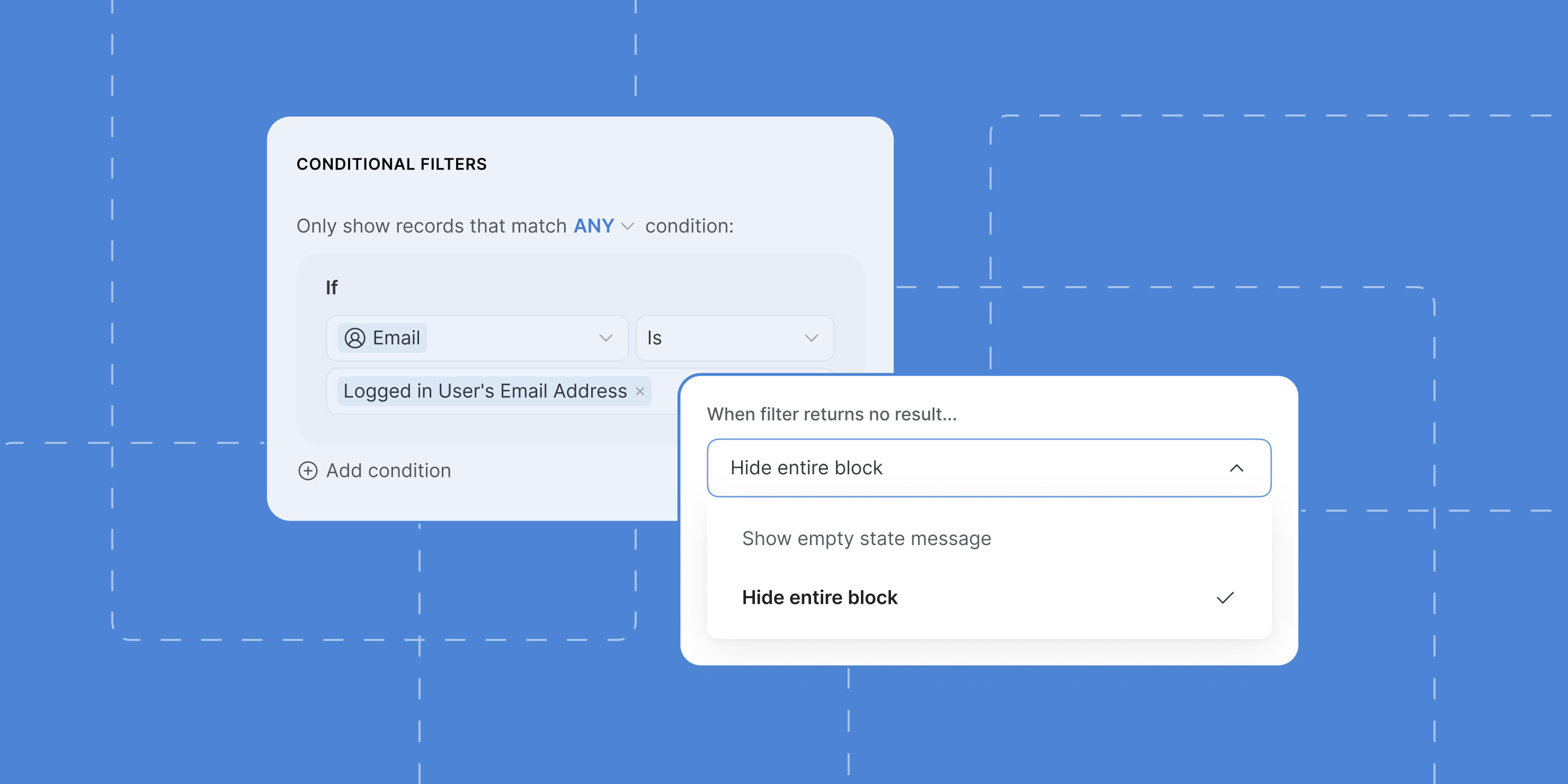
Personal access tokens play a vital role in maintaining security and controlling access within Softr. As businesses rely more on automated processes and external integrations, ensuring secure access becomes paramount. PATs provide a layer of protection by allowing granular control over who can access specific resources and what actions they can perform.
For example, if you're integrating Softr with a payment gateway or another sensitive service, using PATs ensures that only authorized users can access these resources. This reduces the risk of unauthorized access and potential data breaches.
Read also:Imurdrug Onlyfans Exploring Content Success And Everything You Need To Know
Benefits of Using PATs in Softr
- Enhanced Security: PATs reduce the risk of exposing sensitive credentials.
- Granular Control: You can assign specific permissions to different users or integrations.
- Improved Accountability: Each token can be traced back to a specific user or integration, making it easier to track activity.
How Do Personal Access Tokens Work?
Personal access tokens function by acting as a substitute for traditional login credentials. When you generate a PAT, the platform assigns it a unique string of characters that can be used to authenticate API requests or grant access to specific resources. These tokens are typically stored securely and can be revoked or updated as needed.
When a request is made using a PAT, the platform verifies the token against its database to ensure it is valid and has the necessary permissions. If the token is valid, the request is processed; otherwise, it is denied. This process ensures that only authorized users or integrations can access sensitive data or perform specific actions.
Steps in the PAT Authentication Process
- Token Generation: Create a new PAT within the platform's settings.
- Token Assignment: Assign the token to a specific user, integration, or API endpoint.
- Token Verification: The platform verifies the token during each request.
- Access Granted/Denied: Based on the token's permissions, access is either granted or denied.
When Should You Use Personal Access Tokens for Softr?
Personal access tokens are particularly useful in scenarios where secure and automated access is required. For example, if you're integrating Softr with a third-party service, using PATs ensures that the integration can access the necessary resources without exposing sensitive credentials.
Additionally, PATs are ideal for managing user roles and permissions within Softr. By assigning tokens with specific scopes, you can ensure that each user has access only to the resources they need, reducing the risk of accidental or malicious actions.
Common Use Cases for PATs in Softr
- API Integrations: Use PATs to securely connect Softr with external APIs.
- Automated Scripts: Automate tasks like data synchronization using PATs for authentication.
- User Management: Control access to specific features or data within your Softr applications.
Security Benefits of Personal Access Tokens
One of the primary advantages of personal access tokens is their ability to enhance security. By replacing traditional login credentials with unique, revocable tokens, PATs reduce the risk of unauthorized access and data breaches. Additionally, their ability to be scoped and time-limited ensures that even if a token is compromised, its impact is limited.
Furthermore, PATs improve accountability by allowing you to trace each token back to a specific user or integration. This makes it easier to monitor activity and identify potential security issues.
How PATs Enhance Security
- Reduced Risk of Credential Exposure: Tokens can be stored securely without exposing sensitive login information.
- Granular Permissions: Assign specific scopes to limit access to sensitive resources.
- Revocable Tokens: Easily revoke tokens if they are compromised or no longer needed.
Step-by-Step Guide to Setting Up Personal Access Tokens in Softr
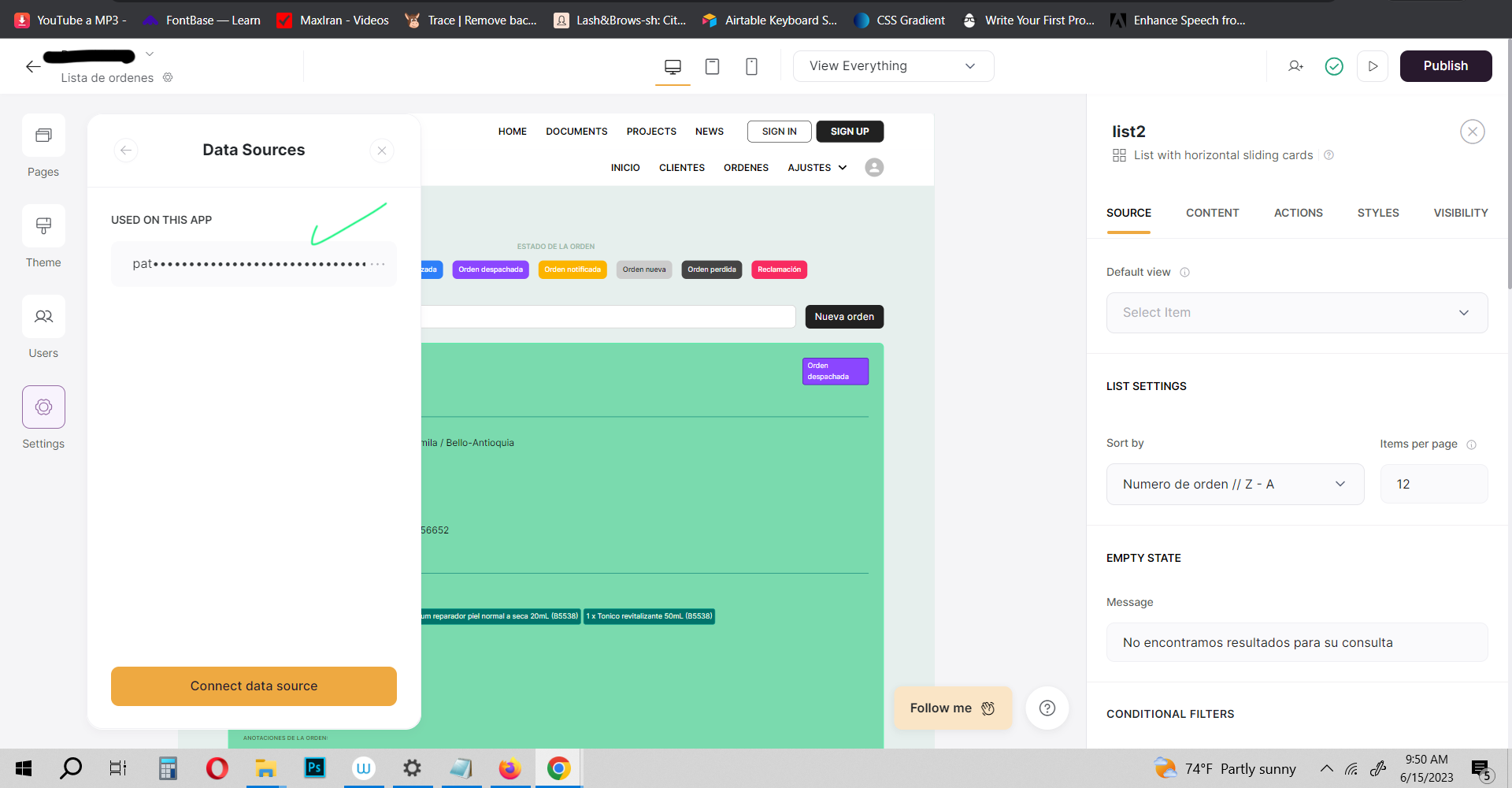
Setting up personal access tokens in Softr is a straightforward process. Follow these steps to generate and manage your tokens effectively:
Access Settings: Log in to your Softr account and navigate to the settings section.
Generate Token: Click on the "Personal Access Tokens" option and generate a new token.
Assign Permissions: Define the scope and permissions for the token based on your requirements.
Store Token Securely: Save the token in a secure location, as it will not be displayed again after the initial generation.
Use Token: Use the token in your API requests or integrations as needed.
Tips for Managing PATs in Softr
- Regularly Review Tokens: Periodically review your active tokens to ensure they are still necessary.
- Limit Token Lifespan: Set expiration dates for tokens to minimize the risk of long-term exposure.
- Document Token Usage: Keep a record of which tokens are used for what purposes to improve accountability.
Alternatives to Personal Access Tokens
While personal access tokens are a popular choice for secure access management, there are alternative methods you can consider depending on your specific needs. Some of these alternatives include:
- API Keys: Similar to PATs, API keys are used for authenticating API requests but may lack the granular control offered by tokens.
- OAuth Tokens: OAuth provides a more robust authentication framework, especially for multi-user applications.
- Username and Password: Traditional login credentials can still be used in some cases but are generally less secure than PATs.
Common Issues and Troubleshooting
While personal access tokens are a powerful tool, they can sometimes present challenges. Below are some common issues and their solutions:
- Token Expiration: Ensure that tokens are renewed before they expire to avoid disruptions in service.
- Permission Errors: Verify that the token has the correct scopes and permissions for the requested actions.
- Token Compromise: If a token is compromised, revoke it immediately and generate a new one.
Best Practices for Managing Personal Access Tokens
To ensure the effective and secure use of personal access tokens, follow these best practices:
- Limit Token Scope: Assign the minimum necessary permissions to each token.
- Store Tokens Securely: Use secure storage solutions to protect your tokens from unauthorized access.
- Regularly Audit Tokens: Periodically review your active tokens and revoke any that are no longer needed.
Conclusion
In conclusion, personal access tokens are an essential tool for managing secure access in platforms like Softr. By understanding their role and implementing them effectively, you can enhance the security and functionality of your applications. Whether you're integrating third-party tools, automating processes, or managing user roles, PATs provide the flexibility and control you need to succeed.
We encourage you to take action by exploring the use of personal access tokens in your Softr projects. Leave a comment below to share your experiences or ask questions, and don't forget to explore other articles on our site for more insights into no-code development and security best practices.